The folks at Let's Encrypt know that end-to-end encryption is a necessity in this day and age, and encourage people to secure their websites by providing the tools you need for free. This tutorial will guide you through the steps required to secure your Windows/IIS-hosted websites and automate renewals for wildcard domains.
If you're hosting a website which includes any kind of form, or some other functionality which handles user-submitted data, you should be transmitting this data over a secure connection. SSL encryption ensures that data sent between two points is less likely to be intercepted and read by "man in the middle" styles of attack. SSL certificates are offered as part of most web hosting or domain packages, but these often come at an extra cost - in this guide we'll go over setting one up for free on a Windows-hosted IIS website.
Assumptions
- You have administrative permissions on a Windows server
- You already have a website running on IIS
- You have a domain with permission to create and modify records
- You have permission to modify firewall rules, or port 443 is open to inbound traffic
The standard use case for a basic website certificate just secures a specific domain, such as "tomjones.dev", however, it's useful to generate certificates which can cover subdomains as well, both current and future, without having to create individual certificates each time. Common examples may include an API (e.g. "api.tomjones.dev"), or an ecommerce store (e.g. "shop.tomjones.dev"). As such, we'll be opting for the more advanced configuration which allows us to secure a wildcard (*.) domain.
A scheduled task will be created automatically by following the steps in this article. This task runs daily to check the status of renewals and renew certificates automatically when necessary.
Please note that the service we'll be using doesn't allow automated renewals for wildcard domains, so if automation is a necessity, ensure you use an absolute domain name (e.g. "tomjones.dev"), rather than a wildcard (e.g. "*.tomjones.dev").
Download and install win-acme
Log into your Windows server, open a browser, navigate to https://www.win-acme.com/, download the latest version to your machine and double click the icon to start. Alternatively, if you have the .NET SDK installed on the server, you can achieve the same result by opening up a PowerShell and entering the following two commands:
1dotnet tool install win-acme --global2wacs.exe
Generate a certificate
As this guide assumes you have a HTTP website set up and running, inbound traffic on port 80 should already be permitted through the firewall and there should be a a "http" binding configured. If not, ensure you add the rule to your server's firewall before attempting these steps, and add the binding to confirm your website is accessible to HTTP traffic.
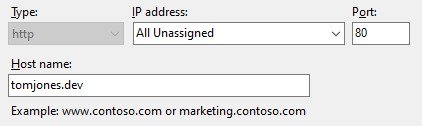
Note: Some top-level domains, such as ".dev", are configured to only work over HTTPS, and will be inaccessible with only a HTTP binding.
Configure the certificate using wacs [INCOMPLETE]
Open wacs.exe and select "M" to create a certificate with full options, the select the option to read bindings from IIS. Continue through the steps choosing the default highlighted options until you get to the domain verification step.
We will need to verify using DNS since we're creating a wildcard certificate. For this purpose, win-acme provides plugins for a variety of providers. I use Route53 as my DNS so the following steps will cover those steps, but should be fairly similar for the others.
Please note that using this method requires changes to IAM permissions in AWS, and can only therefore be applied to an EC2 instance provided by AWS.
Download and configure the DNS plugin...[INCOMPLETE]
https://www.win-acme.com/reference/plugins/validation/dns/route53
Create an IAM role
Confirm the certificate has been properly configured
If everything has been set up correctly so far, navigating to "http://your-website.tld" will still show the old, unsecured website, however, if you try to navigate to "https://your-website.tld" and are presented with a HTTP 403 (Forbidden) error page you will need to follow the steps in the next section to allow HTTPS traffic.
Allow inbound traffic using port 443
Inbound HTTPS traffic needs to be permitted through your server's firewall in order to ensure visitors can access your website once it has been secured with an SSL certificate.
Locate the firewall settings for your server, and add an inbound rule allowing any IP to access port 443 (SSL). If your server is hosted on an AWS EC2 instance, the ruleset is defined in the "security group" attached to your instance - details of how to configure these can be found at https://docs.aws.amazon.com/AWSEC2/latest/WindowsGuide/ec2-security-groups.html.
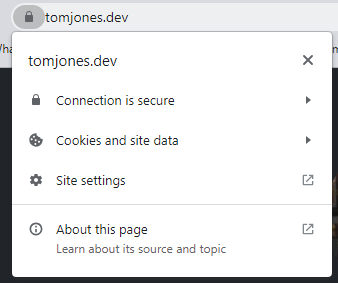
Once the firewall was been configured to allow HTTPS traffic, your website should load and you can confirm the certificate details by clicking on the the lock icon beside the address bar.